If you’ve just installed Anaconda / Spyder IDE (available here for personal use) in Windows find it’s not launching, and neither is the Anaconda launcher, and you have a previous installation of Python e.g. Python 2+<3, remove Python 2.X from your Windows PATH variables and retry opening it.
To do this, right click on ‘My Computer’,
select Properties to bring up System Properties and
click ‘Advanced System Settings’.
Agree to the UAC prompt and click ‘Environment Variables’ then look for Python references anywhere, edit and delete as required.
Retry launching Anaconda/Spyder and it will now work.
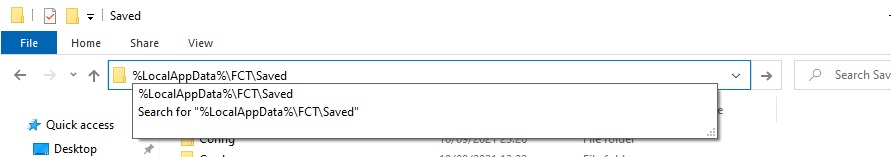
If this doesn’t work, open a command prompt (Type cmd/enter from the start menu), navigate to the Anaconda installation (in Windows 10, ‘cd c:\programdata\anaconda3\” and try launching anaconda or spyder (.\scripts\spyder.exe) and noting any error messages that appear which can then be googled for the relevant fixes.
Hope this helps!
Garreth